一、介绍
1. 什么是白加黑
通俗的讲白加黑中的白就是指被杀软列入到可信任列表中的文件。比如说微软自带的系统文件或者一些有有效证书签名的文件,什么是微软文件,或者什么是有效签名文件在后面我们会提到他的辨别方法。黑就是指我们自己的文件,没有有效证书签名,也不是微软文件。通常这种文件会被杀软加入到可疑名单中。
2. 白加黑的作用是什么
在很多的杀软中会对白文件的操作进行放行,如果我们将黑程序和白程序在一个进程中是否就可以绕过一些杀软的检测。
二、如何挖掘利用白文件
1. 思考->解决
问:如果我们想要将我们的黑程序载入到白文件中有什么办法?
答:通常情况下我们可以利用注入去将一个程序执行到另外的程序中。
问:在程序执行的开始,如何加载一个DLL。
答:程序加载的时候会优先加载当前文件夹下的文件下的DLL,当然这些DLL要存在于可执行程序的导入表中。
2. 挖掘白文件
首先我们先去找几个有签名的文件或者微软的可执行文件。
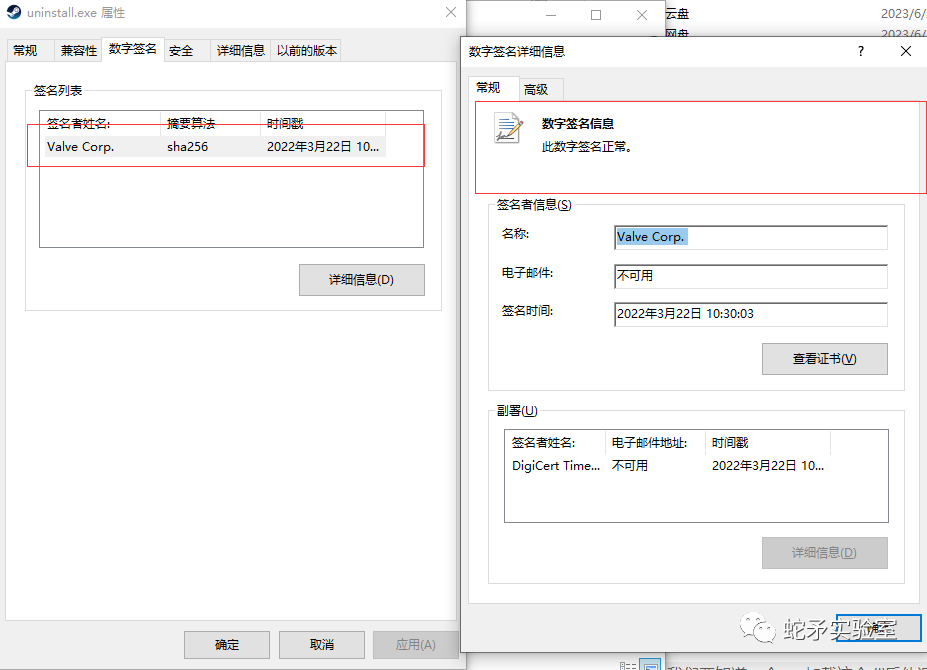
下图就是签名的鉴别方式。必须是正常数字签名才行。
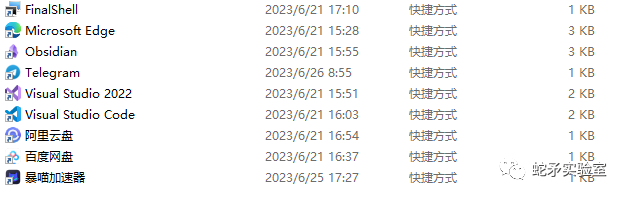
这里有一些我们常用的软件也可以利用,我们尽量去看看目录里面体积小的文件,这样方便我们在攻击的时候投入。
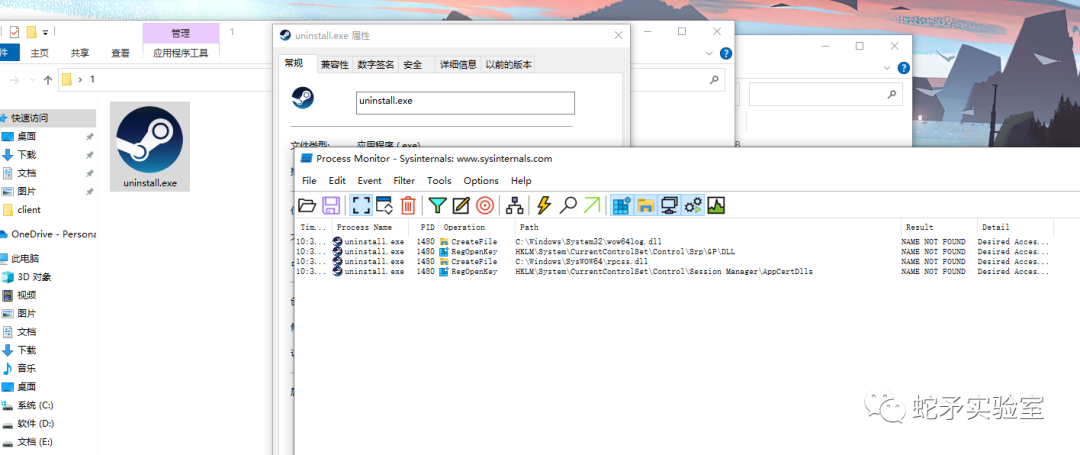
这里我们在steam中找到一个uninstall.exe的exe,用ProcessMonitor可以监控到他执行的时候加载了一个
“C:WindowsSystem32wow64log.dll” ,那么我们是否可以写一个这个dll放到和他在相同的目录下让他加载我们的wow64log.dll不去加载System32下的wow64log.dll呢?
那么我们去尝试下
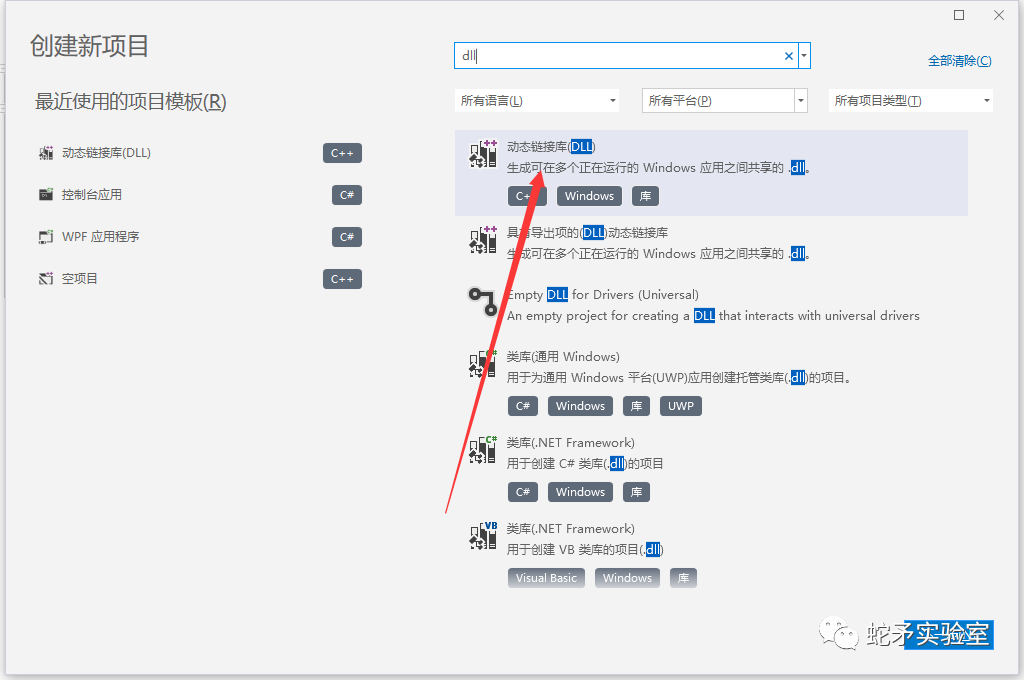
3. 如何构造wow64log.dll
首先我们要知道一个exe加载这个dll后他调用了哪些函数,我们要去伪造这些函数,不然他肯定是加载不起来的。有很多方式可以查看比如说LordPe,或者说VS带有的dumpbin。这里我们用dumpbin来看下白程序的导入表,看看wow64log.dll用到了哪些函数。
C:\Users\Administrator\Desktop\1>dumpbin /imports uninstall.exe
Microsoft (R) COFF/PE Dumper Version 14.36.32535.0
Copyright (C) Microsoft Corporation. All rights reserved.
Dump of file uninstall.exe
File Type: EXECUTABLE IMAGE
Section contains the following imports:
KERNEL32.dll
408070 Import Address Table
408614 Import Name Table
0 time date stamp
0 Index of first forwarder reference
30B SetCurrentDirectoryW
161 GetFileAttributesW
16A GetFullPathNameW
356 Sleep
1DF GetTickCount
56 CreateFileW
163 GetFileSize
271 MoveFileW
31A SetFileAttributesW
17E GetModuleFileNameW
46 CopyFileW
B9 ExitProcess
314 SetEnvironmentVariableW
1F4 GetWindowsDirectoryW
1D6 GetTempPathW
111 GetCommandLineW
1E8 GetVersion
315 SetErrorMode
390 WaitForSingleObject
142 GetCurrentProcess
39 CompareFileTime
20A GlobalUnlock
203 GlobalLock
6F CreateThread
171 GetLastError
4E CreateDirectoryW
69 CreateProcessW
2C5 RemoveDirectoryW
3C3 lstrcmpiA
1D4 GetTempFileNameW
3A4 WriteFile
3C6 lstrcpyA
3C7 lstrcpyW
270 MoveFileExW
3BE lstrcatW
1C2 GetSystemDirectoryW
1A0 GetProcAddress
17F GetModuleHandleA
1FF GlobalFree
1F8 GlobalAlloc
1B6 GetShortPathNameW
2DC SearchPathW
3C4 lstrcmpiW
31F SetFileTime
34 CloseHandle
BD ExpandEnvironmentStringsW
3C1 lstrcmpW
150 GetDiskFreeSpaceW
3CD lstrlenW
3CA lstrcpynW
15A GetExitCodeProcess
D5 FindFirstFileW
DD FindNextFileW
84 DeleteFileW
31B SetFilePointer
2B5 ReadFile
CE FindClose
274 MulDiv
275 MultiByteToWideChar
3CC lstrlenA
394 WideCharToMultiByte
19D GetPrivateProfileStringW
3AA WritePrivateProfileStringW
F8 FreeLibrary
254 LoadLibraryExW
182 GetModuleHandleW
USER32.dll
408198 Import Address Table
40873C Import Name Table
0 time date stamp
0 Index of first forwarder reference
15C GetSystemMenu
248 SetClassLongW
1AE IsWindowEnabled
C2 EnableMenuItem
283 SetWindowPos
15A GetSysColor
16F GetWindowLongW
24D SetCursor
1BD LoadCursorW
38 CheckDlgButton
13C GetMessagePos
1B9 LoadBitmapW
1C CallWindowProcW
1B1 IsWindowVisible
42 CloseClipboard
24A SetClipboardData
C1 EmptyClipboard
1F6 OpenClipboard
2D8 wsprintfW
231 ScreenToClient
174 GetWindowRect
15D GetSystemMetrics
254 SetDlgItemTextW
114 GetDlgItemTextW
1E3 MessageBoxIndirectW
2F CharPrevW
2A CharNextA
2D7 wsprintfA
A2 DispatchMessageW
201 PeekMessageW
10C GetDC
22A ReleaseDC
C4 EnableWindow
193 InvalidateRect
240 SendMessageW
8F DefWindowProcW
D BeginPaint
FF GetClientRect
E2 FillRect
C6 EndDialog
219 RegisterClassW
29A SystemParametersInfoW
61 CreateWindowExW
F9 GetClassInfoW
9F DialogBoxParamW
2C CharNextW
E1 ExitWindowsEx
99 DestroyWindow
1C1 LoadImageW
27A SetTimer
287 SetWindowTextW
204 PostQuitMessage
292 ShowWindow
111 GetDlgItem
1AD IsWindow
281 SetWindowLongW
E5 FindWindowExW
2A4 TrackPopupMenu
9 AppendMenuW
5E CreatePopupMenu
BF DrawTextW
C8 EndPaint
56 CreateDialogParamW
23F SendMessageTimeoutW
257 SetForegroundWindow
GDI32.dll
40804C Import Address Table
4085F0 Import Name Table
0 time date stamp
0 Index of first forwarder reference
20E SelectObject
216 SetBkMode
3D CreateFontIndirectW
23C SetTextColor
8F DeleteObject
16B GetDeviceCaps
29 CreateBrushIndirect
215 SetBkColor
SHELL32.dll
40817C Import Address Table
408720 Import Name Table
0 time date stamp
0 Index of first forwarder reference
C3 SHGetSpecialFolderLocation
BD SHGetPathFromIDListW
7A SHBrowseForFolderW
AD SHGetFileInfoW
10B ShellExecuteW
9B SHFileOperationW
ADVAPI32.dll
408000 Import Address Table
4085A4 Import Name Table
0 time date stamp
0 Index of first forwarder reference
1D7 RegDeleteKeyW
22F SetFileSecurityW
1AC OpenProcessToken
150 LookupPrivilegeValueW
1C AdjustTokenPrivileges
1ED RegOpenKeyExW
1E2 RegEnumValueW
1D9 RegDeleteValueW
1CB RegCloseKey
1D2 RegCreateKeyExW
205 RegSetValueExW
1F8 RegQueryValueExW
1E0 RegEnumKeyW
COMCTL32.dll
408038 Import Address Table
4085DC Import Name Table
0 time date stamp
0 Index of first forwarder reference
34 ImageList_AddMasked
Ordinal 17
38 ImageList_Destroy
37 ImageList_Create
ole32.dll
4082A0 Import Address Table
408844 Import Name Table
0 time date stamp
0 Index of first forwarder reference
105 OleUninitialize
EE OleInitialize
65 CoTaskMemFree
10 CoCreateInstance
Summary
21000 .data
36000 .ndata
2000 .rdata
13000 .rsrc
7000 .text
C:\Users\Administrator\Desktop\1>
可以发现这里面并没有wow64log.dll这个导入dll,那么他有可能是动态加载的,也有可能是默认加载的。这样我们就不需要考虑这个dll的导出函数了,直接伪造一个dll即可。
首先我们要知道这个可执行程序32位还是64位,我们可以用DIE或者x64dbg去查看。
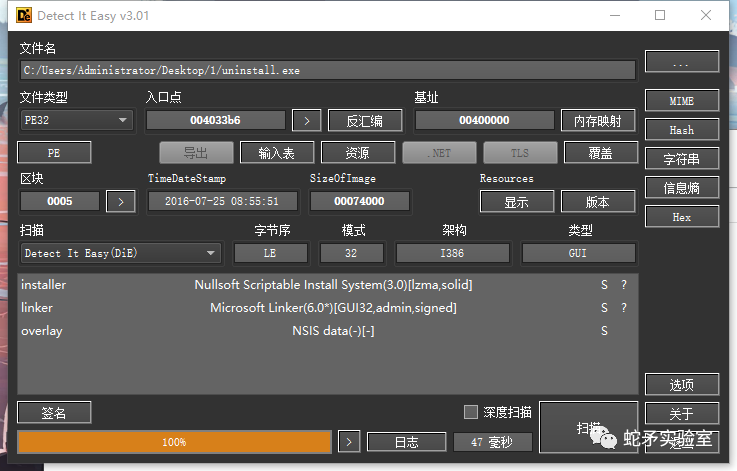
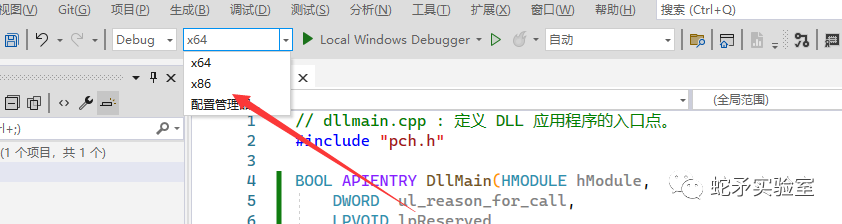
这里看得出来是PE32,那么我们要构造的dll也就是32位的dll。
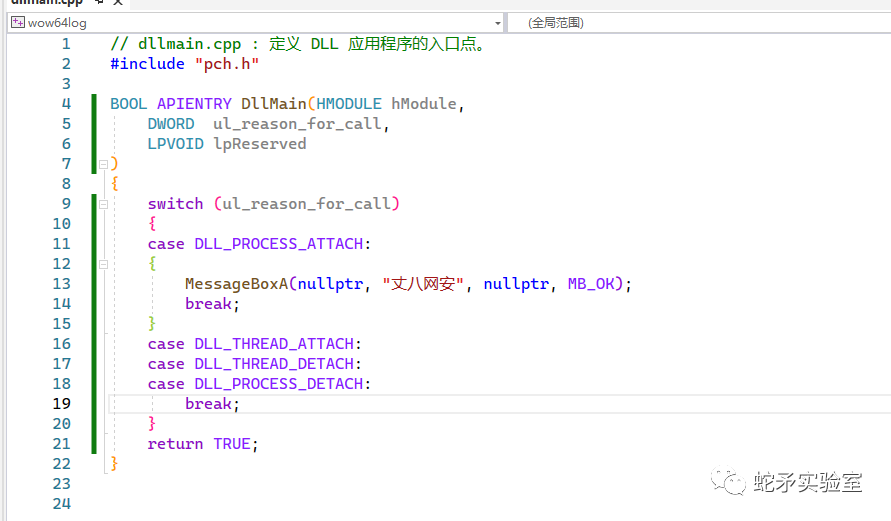
我们在进程附加的时候去弹出一个信息框
这里我们选择和程序对应的架构。X86编译出来就是PE32。
编译好之后我们和可执行文件放到同目录下去执行文件即可。
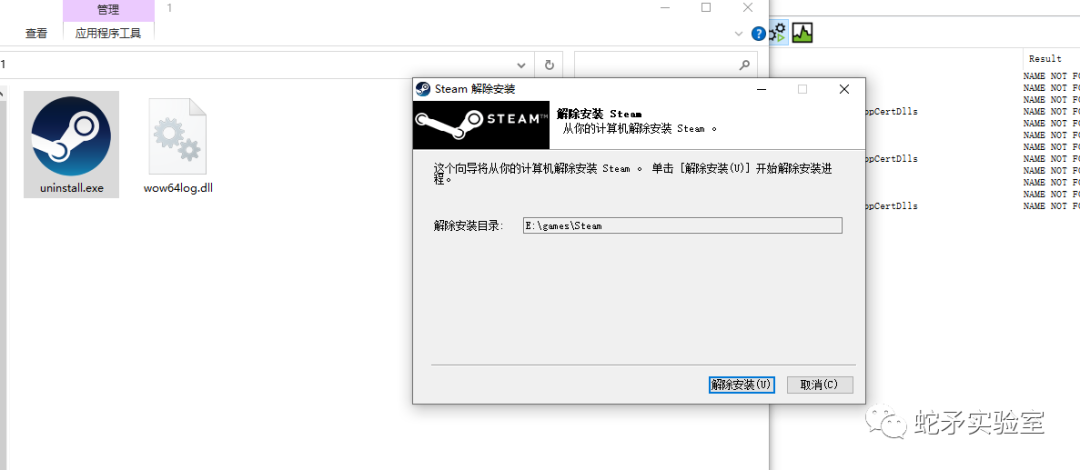
很遗憾我们并没有去加载成功我们的dll,此时就说明此文件不是我们可以利用的程序,我们需要去更换程序。我们需要继续去以上步骤去重新找白程序文件。

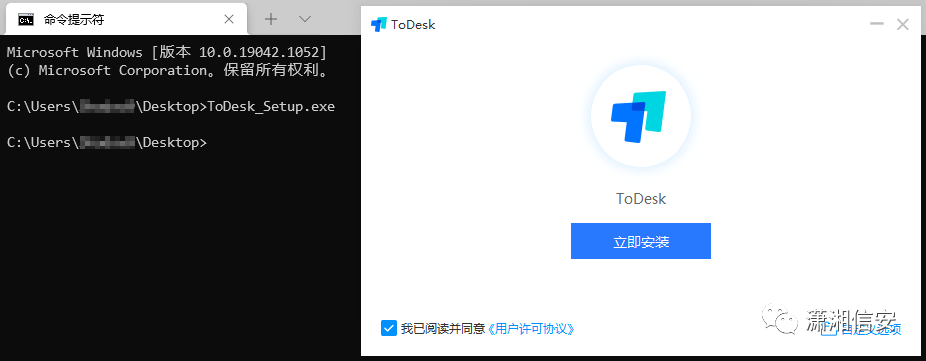
这里我们找到一个企业微信里面的exe我们再去尝试一下。
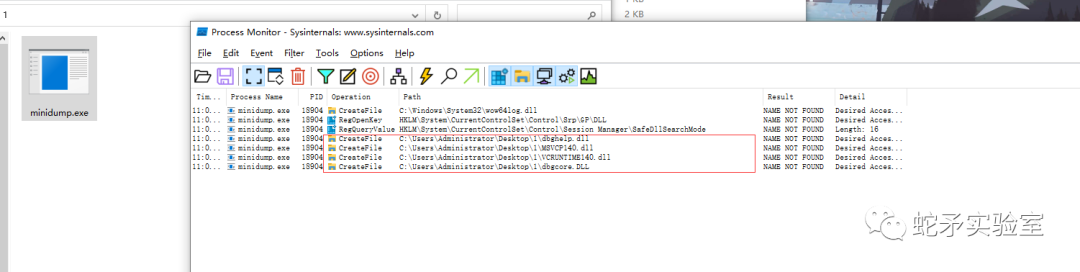
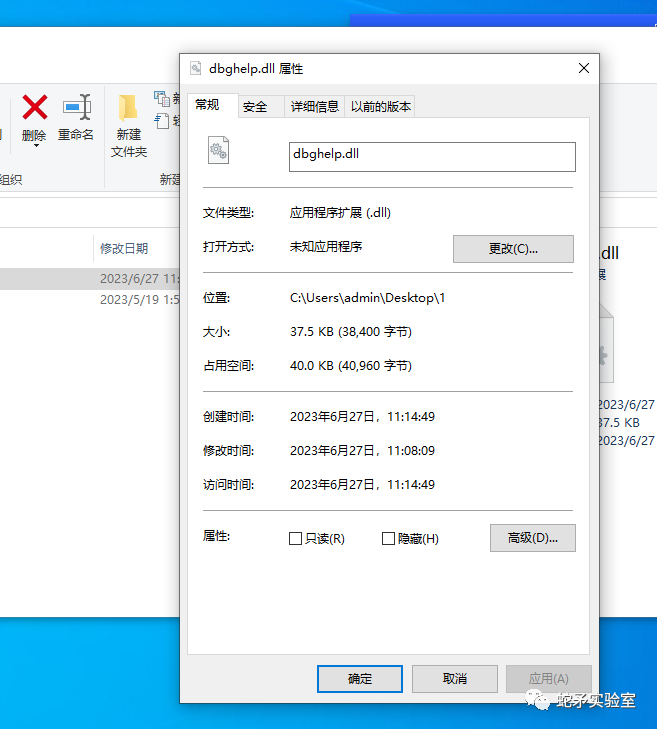
可以看出我们先加载了dbghelp.dll我们将我们之前的文件名字改成这个名字看看是否可以运行。
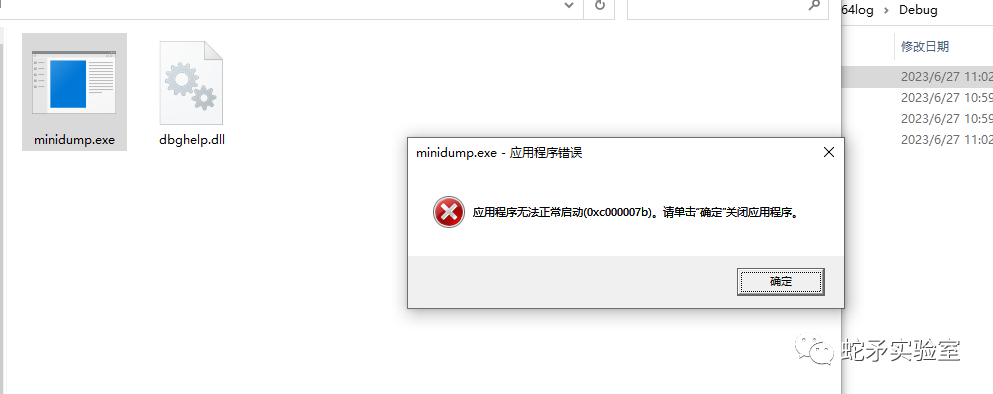
此时看到这个图,不要认为我们又要换白程序了,报错是成功的一大步,到这里就说明我们已经成功百分之90了,这里的问题是我们dll虽然有了但是程序加载我们的dll后调用的函数我们并没有提供,好的我们用dumpbin来看下。
C:\Users\Administrator\Desktop\1>dumpbin /imports minidump.exe
Microsoft (R) COFF/PE Dumper Version 14.36.32535.0
Copyright (C) Microsoft Corporation. All rights reserved.
Dump of file minidump.exe
File Type: EXECUTABLE IMAGE
Section contains the following imports:
dbghelp.dll
403108 Import Address Table
403A6C Import Name Table
0 time date stamp
0 Index of first forwarder reference
1D MiniDumpWriteDump
这里可以看到我们的dll需要一个MiniDumpWriteDump这个函数,我们在代码中添加一下。
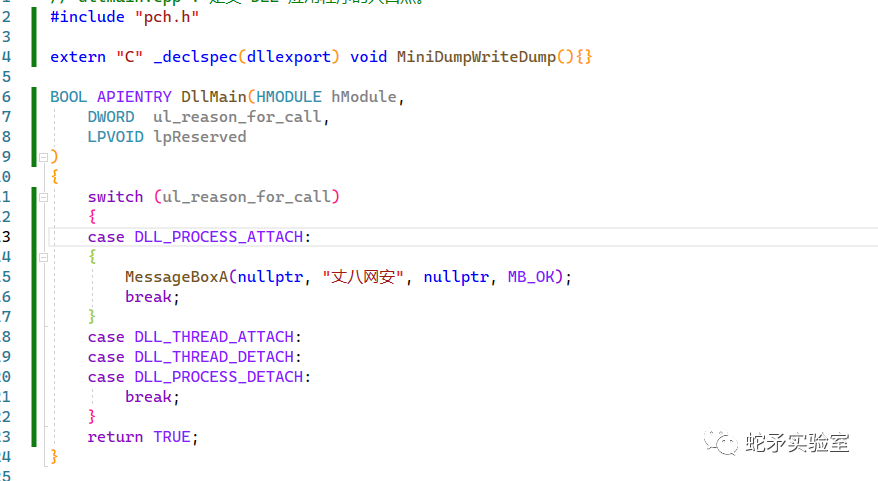
我们编译再去执行下。
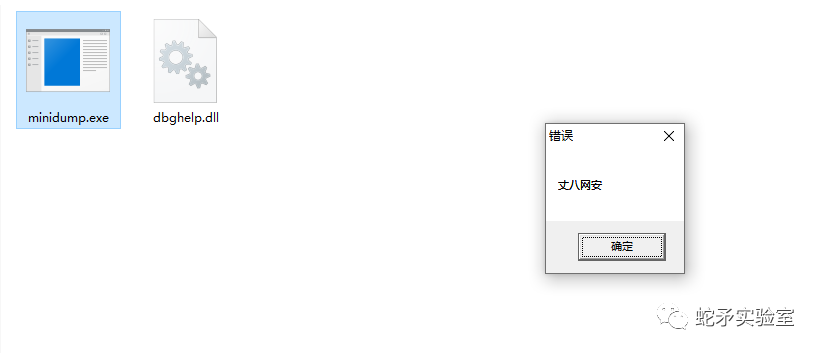
这里我们就可以弹出我们的信息框了。
三、如何检测是否为白加黑程序
1. 杀软检测
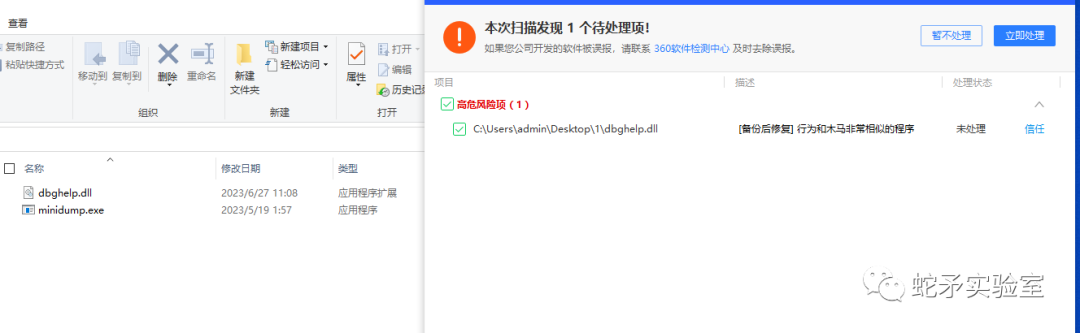
杀软很容易检测的这些简单的白加黑文件,因为我们找的黑dll是系统自带的文件,杀软只需对比Hash就可过了出是不可信文件,一般情况下也不会有程序去伪造系统的dll文件。(这里也好解决我们只需要找一些加载不是系统文件的白程序即可。)
2. 手动检测
手动检测的方式也很简单,我们只需要多注意这种exe只带有一个dll的文件,因为如果是木马的话他一般不会有很多文件,我们可以dll右键属性看看是否有签名,如果没有就很可疑,如果有的话看看签名是否有效,这里也可以用代码去代替这个过程。
以上两种都可以怀疑此程序是可疑程序。
—END—
丈八网安蛇矛实验室成立于2020年,致力于安全研究、攻防解决方案、靶场对标场景仿真复现及技战法设计与输出等相关方向。团队核心成员均由从事安全行业10余年经验的安全专家组成,团队目前成员涉及红蓝对抗、渗透测试、逆向破解、病毒分析、工控安全以及免杀等相关领域。
转发:丈八网安蛇矛实验室
1.本站上传的源码,均为平台购买,作者提供,网友推荐,互联网平台整理而来,请下载后24小时内删除。如有需要,请购买正版.
2.请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任。
3.站内资源若侵犯了您的合法权益,请指出本站立即改正。
4.上述内容仅供学习参考及技术交流之用,未经相关的知识产权权利人同意,用户不得进行商业使用。
5.保姆式服务,百分百售后!

评论(2)
有偿找大佬帮忙,合法,事后必重谢!
酬谢:别人连接我家里WIFI,我想查看对方的手机内容。573243910@qq.com